A group of hackers with a history of targeting healthcare organizations executed a prosperous ransomware attack in the week in the University of California, San Francisco.
UCSF confirmed it absolutely was the objective of an “illegal intrusion” but declined to spell out which percentage of its IT network may have been compromised. Researchers with the university are among those leading American antibody testing and numerous studies for possible coronavirus treatments, including research on anti-malarial drugs touted by President Donald Trump like a possible remedy, then refuted by scientists.
If any, information may have been compromised,” Farley said in a statement, the university has alerted security experts and law enforcement of the attack, which didn’t affect its patient care operations, said Peter Farley, a director of communications at UCSF.“With their assistance, we are conducting a thorough assessment of the incident, including a determination of what. “In order to preserve the integrity of the investigation, we must limit whatever we can share at the moment.”
Continue reading: Malaria Drug Taken by Trump Provides No Covid-19 ProtectionThe NetWalker hackers claimed credit for that attack on their darkweb blog. The post devoted to UCSF seemed to be copy and pasted from the university’s homepage promoting its work towards healthcare.Attack groups often post data samples to prove the achievements their breach. In such a case, their blog posted four screenshots, including of two files accessed with the attackers. The files’ names, seen by Bloomberg around the darkweb, contain possible references towards the US Centers for Disease Control and Preventiondepartments and Prevention central to the university’s coronavirus research.
The blog includes a flashing-red timer threatening “secret data publication” by June 8 Pacific Time if payment isn’t received. The post doesn’t mention the price of ransom demanded.
Generally in most ransomware cases, payment is followed by the exchange of a decryption key that enables victims to gain access to their files. When victims don’t pay, which is usually the case if they have backup copies to regenerate their data, attack groups sometimes publish the most sensitive data in hopes of coaxing payment.
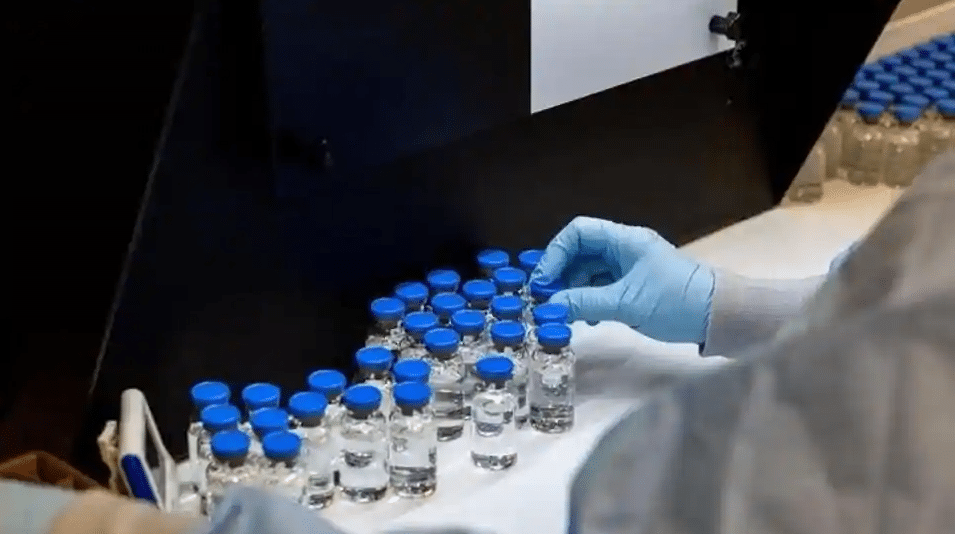
Also for possibly lucrative intellectual property, like valuable research on a cure for Covid-19, even though hackers are increasingly targeting institutions like UCSF not only for ransomware payments themselves. UCSF has engaged in extensive sampling and anti-body testing, including in the experimental anti-viral drug remdesivir, which contains shown signs and symptoms of being effective at the start of the Covid-19 life-cycle.
The US was hit by a record number of ransomware attacks in 2019 and attackers have revealed little symbol of relenting in 2020, when users spent more time on less secure networks while working from home. According to the cyber research firm Emsisoft, in 2019, at least 966 government agencies, schools and healthcare providers were attacked at a cost of more than $7.5 billion. Among those were almost 90 universities.Netwalker ransomware was initially introduced and operated by the criminal cyber group dubbed Circus Spider by CrowdStrike Inc. Since September 2019, Netwalker ransomware has been actively used by criminal actors with links to malware including Mailto, Koko, and KazKavKovKiz.“The use of Covid-19 lures and targeting entities in the healthcare sector indicate that the operators of Netwalker are taking advantage of the global pandemic in order to gain notoriety and increase their customer base,” according to a Crowdstrike research report.